Related posts
Marc-Andre ChartrandMarch 05 20263 Min Read
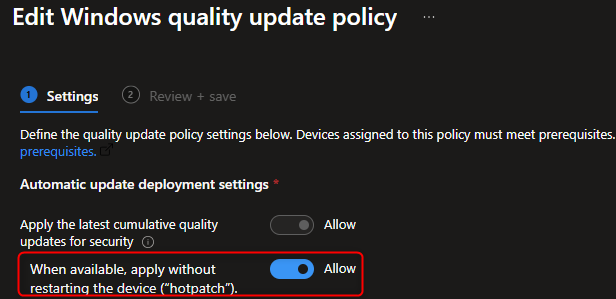
How to Configure Windows Hotpatch with Intune
Microsoft has introduced Hotpatch for Windows 11 Enterprise, a feature that allows you to apply...

Jonathan LefebvreNovember 14 20259 Min Read
Step-by-Step SCCM 2509 Upgrade Guide
Microsoft has released the second SCCM version for 2025, as the release cadence is now reduced to... Ana_Ibarro.rar
Jonathan LefebvreSeptember 08 20257 Min Read
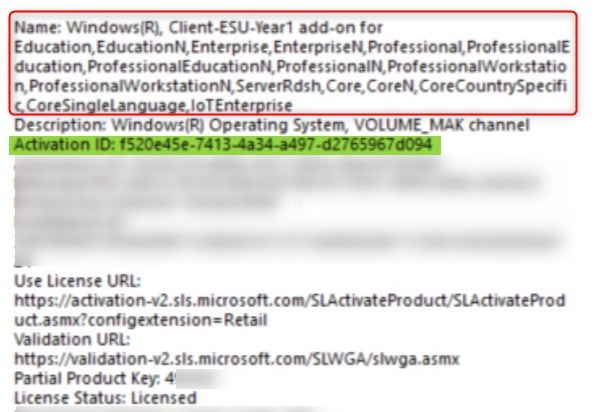
Deploy Windows 10 Extended security update key (ESU) with Intune or SCCM
With Windows 10 support ending October 14, 2025, organizations face a critical choice: upgrade to... To help me develop a detailed write-up (whether



To help me develop a detailed write-up (whether for forensics, malware analysis, or general documentation), could you provide some context or perform a few basic checks on the file? Specifically:
: Where did this file come from? (e.g., a specific CTF platform like Hack The Box, a phishing simulation, or a real-world incident).
: Are you looking for a technical analysis (what the file does), a forensic timeline (how it got there), or a walkthrough for a puzzle?
If you can share the or any extracted strings , I can dive much deeper into the analysis for you. What is the primary goal of the write-up you need? AI responses may include mistakes. Learn more
: Does the RAR archive contain specific types of files (e.g., .exe , .lnk , .pdf , or memory dumps)?
: If you have access to the file, what are its MD5/SHA256 hashes ? I can use these to look up technical signatures even if the filename is unique.